[ad_1]
Web3 represents a brand new model of the web that might leverage blockchain know-how, good contracts, and dApps for decentralization. It goals to create a safer, democratic, and clear variant of the online. As in comparison with conventional internet purposes, web3 apps depend upon a distributed community of nodes for validation of transactions alongside implementing further features.
Nonetheless, safety has emerged as a serious concern for web3, primarily attributable to using good contracts. Even a complete web3 safety audit might miss notable vulnerabilities reminiscent of integer overflow assaults, denial-of-service assaults, and reentrancy assaults. Moreover, the decentralization in web3 apps additionally presents a formidable safety concern because the apps wouldn’t have a centralized server or authority for caring for safety. As well as, web3 is essentially open-source in nature, thereby enabling hackers to entry the code and unravel vulnerabilities.
You is perhaps questioning concerning the resolution to the web3 safety points as they might impose a large burden of economic losses. Curiously, you will discover a dependable reply for avoiding web3 safety points in penetration testing. Penetration testing for web3 apps may also help in evaluating dApps good contracts alongside different web3 parts for figuring out vulnerabilities and potential websites of assault.
It’s essential to perceive the significance of web3 penetration testing, its totally different variants, and the methodology for penetration testing in web3 purposes. Allow us to be taught extra about penetration testing in web3 and the way it works.
What’s Web3 Penetration Testing?
Penetration testing or pentest in web3 is just like the approaches adopted for safety testing in web2 purposes. Anybody who needs to be taught Web3 ought to know that web3 growth has gained important enchancment in momentum. Many firms and builders wish to capitalize on the web3 applied sciences and rules for embracing the decentralized internet. Internet 3.0 is a revolutionary paradigm that modifications the functioning of various industries, reminiscent of finance, gaming, and provide chain administration.
The variety of web3 startups has been rising steadily alongside the repeatedly increasing volumes of funding in web3. Nonetheless, the rising recognition of web3 additionally paves the trail for web3 vulnerabilities that may result in irreversible penalties. For those who undergo the latest reviews about web3 safety, you will discover that web3 safety points trigger large losses.
For instance, the overall monetary losses attributable to web3 safety breaches in 2022 have been over $3.5 billion. As well as, reviews have identified that the losses attributable to web3 safety breaches within the first six months of 2023 have crossed $650 million. Due to this fact, it is very important search for proactive strategies that may assist safeguard person information, funds, and integrity of blockchain structure.
Penetration testing can outperform essentially the most highly effective web3 safety instruments for safeguarding web3 apps and customers. Penetration testing in web3 is a complete course of for evaluating the safety of good contracts, blockchain networks, and dApps. The beneficial method for penetration testing in web3 focuses on simulation of real-world assaults for figuring out weaknesses and vulnerabilities within the web3 panorama.
Study the basics, challenges, and use instances of Web3.0 blockchain from Introduction To Internet 3.0 E-Guide
Distinction between Conventional Penetration Testing and Web3 Penetration Assessments
Web3 penetration assessments differ from conventional penetration testing in numerous methods. The primary distinction is clear in the truth that web3 apps run in decentralized environments, which presents particular safety dangers. For instance, good contract vulnerabilities might open new surfaces of assault for hackers. As well as, web3 apps additionally observe totally different protocols and interfaces, reminiscent of JSON-RPC, which requires specialist testing information and tools.
One other differentiating issue between web3 and web2 penetration assessments is using blockchain know-how. Whenever you be taught web3, you will discover out that web3 apps function inherent safety traits. Nonetheless, the inherent safety traits couldn’t safeguard web3 apps towards vulnerabilities within the code or approaches for interacting with blockchain.
Most essential of all, you will need to additionally deal with the need of particular regulatory necessities for web3 throughout penetration testing. For instance, DeFi purposes should adjust to monetary laws of their seek for vulnerabilities.
Excited to be taught concerning the essential vulnerabilities and safety dangers in good contract growth, Enroll now within the Good Contracts Safety Course
Working of Penetration Testing in Web3
It’s essential to know concerning the superb steps for implementation of penetration testing in web3 to make sure one of the best outcomes. Efficient penetration testing in web3 requires complete planning and growing the scope of the testing mission. Efficient planning for a web3 safety audit might assist in identification and analysis of all of the potential vulnerabilities in web3.
A few of the essential levels within the starting stage embrace establishing the aims and milestones for the mission. Subsequently, you’d transfer in direction of different levels of penetration testing, reminiscent of understanding the structure and growth of testing technique. Here’s a detailed overview of various steps within the working of web3 penetration assessments.
Outline the Goal of Testing
The primary stage of web3 penetration testing entails clear definition of aims and scope of testing. What are the aims for web3 penetration assessments? You must select the exact targets, reminiscent of dApps, good contracts, or wallets. It is very important perceive the goal atmosphere to make sure the identification and evaluation of all potential vulnerabilities.
Understanding the Structure and Applied sciences
One of many important necessities for profitable penetration testing in web3 factors to your understanding of web3 structure and applied sciences. Web3 apps make the most of totally different instruments and constructions compared to conventional internet purposes. Due to this fact, you will need to be taught web3 structure and know-how with a transparent impression of web3 protocols and interfaces, blockchain know-how, and good contract programming languages.
Curious to develop an in-depth understanding of web3 utility structure? Enroll now within the Web3 Software Growth Course!
Choose the Testing Process
The following stage within the working of penetration assessments entails specification of testing procedures required for the assessments. You possibly can select computerized or handbook web3 assessments. On prime of it, you possibly can discover devoted web3 safety instruments and frameworks for web3 penetration assessments. With a transparent impression of testing aims and the goal atmosphere, you may decide the perfect instruments for profitable penetration assessments.
Put together Your Testing Plan
The ultimate stage within the planning part of the working of penetration assessments in web3 entails preparation of testing plan. After getting outlined the aims, testing strategies, and goal atmosphere, you need to create a testing plan. The testing plan would come with particulars concerning the assessments that you’d implement and the required instruments for a similar.
As well as, you possibly can additionally decide the timing of various assessments. It is very important overview the testing plan and technique with the involvement of all events to acquire authorization from all of the stakeholders.

Forms of Penetration Assessments in Web3
The following subject of dialogue in a information to penetration assessments in web3 focuses on variants of penetration assessments. It is best to word that penetration assessments contain simulation of assaults on web3 techniques and networks for figuring out vulnerabilities. On the similar time, you may come throughout three distinct kinds of internet penetration testing for mitigating web3 safety dangers. Right here is a top level view of the various kinds of penetration assessments concerned in web3.
Exterior Community Penetration Assessments
Exterior community penetration assessments deal with identification of vulnerabilities within the perimeter safeguards for web3 apps. In such kinds of penetration assessments, you will discover simulations of assaults from exterior menace actors. The assessments assist in figuring out the effectiveness of safety controls, reminiscent of internet utility firewalls, firewalls, and intrusion detection techniques. The exterior community penetration check may also help in figuring out essential vulnerabilities reminiscent of weak password insurance policies, open ports, and unpatched software program.
Inside Community Penetration Assessments
The following variant of penetration check for figuring out web3 vulnerabilities is the inner community penetration check. Inside community penetration assessments work by way of simulation of eventualities the place a malicious actor positive factors entry to inner community of web3 apps. Such kinds of penetration assessments deal with figuring out inner vulnerabilities reminiscent of misconfigured entry controls, inappropriate community segmentation, and unsecured databases.
Software Penetration Take a look at
Web3 safety professionals should additionally deal with the applying penetration assessments to find out vulnerabilities within the utility itself. Software penetration assessments are a compulsory addition to web3 safety audit as they assist in recognizing safety points reminiscent of authentication bypass, SQL injection, or cross-site scripting. Software penetration testing is a strong software for safeguarding privateness of person information alongside stopping unauthorized entry.
Need to establish the advantages, challenges, and dangers of web3? Enroll now within the Licensed Internet 3.0 Skilled (CW3P)™ Certification
What are the Different Elements of Web3 Penetration Assessments?
Penetration assessments in web3 don’t deal with simulation of assaults on the perimeter of web3 apps, their inner networks, and the applying itself alone. You may discover different parts in penetration assessments that assist in uncovering a variety of vulnerabilities in web3.
The parts in web3 penetration assessments embrace good contract audits, blockchain testing, pockets software program testing, and DevOps penetration testing. Every element performs an important position in web3 penetration testing by reviewing totally different facets of web3 for safety points. Allow us to check out the essential areas of testing in every element of web3 penetration assessments.
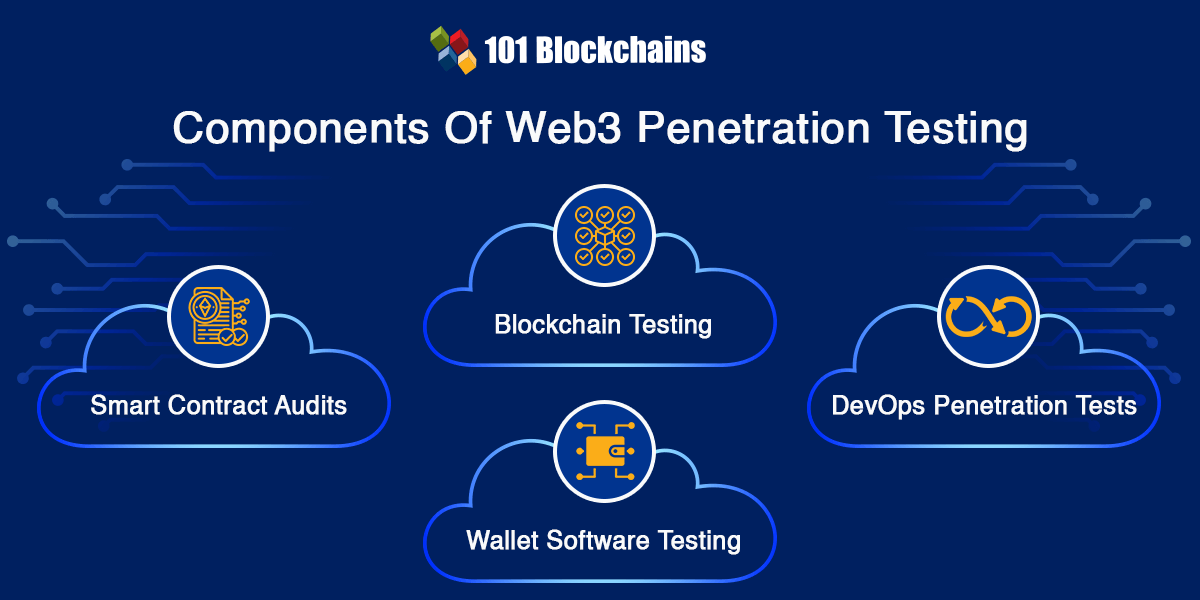
The position of good contracts within the web3 ecosystem can’t be undermined. Good contract audits type an important a part of web3 safety audit process as they assist in testing entry management, transaction order dependency, vulnerability to denial of service, and different asset administration capabilities. The widespread vulnerabilities recognized in good contract audits embrace time manipulation, inadequate entry controls, reentrancy assaults, and quick tackle assaults.
Need to perceive the significance of good contracts audits? Take a look at Good Contract Audit Presentation now!
The kinds of assessments concerned in penetration testing additionally contain blockchain testing, which checks very important parts and potential assault surfaces. Blockchain testing entails analysis of peer-to-peer protocol vulnerabilities, blockchain block parsing, RPC authentication, and safe RPC technique implementation. The widespread assault surfaces recognized in blockchain testing embrace communication interfaces, OS and companies, DevOps, and enter administration.
Pockets Software program Testing
The overview of web3 safety instruments and their significance additionally displays on the need of pockets software program testing. A few of the essential parts concerned in pockets software program testing embrace a person interface, RPC interface, software program dependencies, and transaction administration. As well as, pockets software program testing in web3 penetration assessments additionally opinions the connection of web3 wallets to the third-party nodes and companies.
DevOps Penetration Assessments
One other notable addition among the many kinds of internet penetration testing for web3 factors at DevOps penetration testing. DevOps has develop into an open goal for malicious actors owing to its giant technological footprint and restricted safety controls. As well as, DevOps additionally presents privilege for modification of supply code and deploying it into manufacturing.
The first focus of DevOps penetration assessments is directed towards evaluation of code repository contents and entry privileges, secrets and techniques administration, and entry to manufacturing deployment. DevOps penetration assessments additionally deal with the CI/CD infrastructure alongside authentication for delicate growth parts and developer entry to the manufacturing credentials.
Need to discover an in-depth understanding of safety threats in DeFi tasks? Enroll In DeFi Safety Fundamentals Course now!
What are the Widespread Instruments for Web3 Penetration Assessments?
The particular design of web3 apps requires using specialised instruments for penetration testing in web3. You possibly can depend on web3 safety instruments to assist web3 builders and safety professionals in recognizing and addressing vulnerabilities. Listed below are a few of the hottest.
Mythril is a brilliant contract safety evaluation software for good contracts deployed on Ethereum. It additionally presents the pliability for figuring out totally different web3 vulnerabilities, together with logical errors, reentrancy, and integer overflow or underflow.
EthFiddle is without doubt one of the rising instruments within the web3 safety panorama, as it will possibly assist programmers create and check Ethereum good contracts in a browser-based atmosphere. The safety testing software options totally different simulation instruments alongside an built-in debugger for analysis of good contract safety posture.
One other notable addition amongst instruments for web3 safety factors at ZAP. It really works as a web3 app safety scanner and options totally different plugins for testing web3 apps.
Begin your journey to turning into an knowledgeable in Web3 safety abilities with the steering of business consultants by way of Web3 Safety Knowledgeable Profession Path
Ultimate Phrases
The overview of web3 penetration testing showcases that it is a perfect approach for safety of web3 apps. Web3 safety has emerged as a formidable concern for builders and the broader web3 group attributable to humongous monetary losses. On prime of it, the decentralization and open-source nature of web3 expose web3 apps to various kinds of safety dangers. Customers can discover the perfect countermeasures for avoiding such safety dangers through the use of penetration testing.
It is very important perceive that web3 penetration assessments might deviate from typical penetration testing in sure facets. Nonetheless, the final word goal of penetration assessments revolves round a simulation of assaults to examine the resiliency of internet purposes. Penetration assessments can function a promising increase to the web3 growth panorama and encourage the rise of safe web3 apps.

*Disclaimer: The article shouldn’t be taken as, and isn’t meant to supply any funding recommendation. Claims made on this article don’t represent funding recommendation and shouldn’t be taken as such. 101 Blockchains shall not be liable for any loss sustained by any one that depends on this text. Do your personal analysis!
[ad_2]
Source link
