[ad_1]
Decentralized applied sciences and blockchain-based platforms have emerged as fashionable tendencies within the area of know-how. Does blockchain serve a transformative impression solely within the type of cryptocurrencies and NFTs? The working of blockchain has created the foundations of web3, a brand new model of the web. Web3, dApps, and good contracts are main the world towards a revolutionary future the place customers would have management over their information and on-line experiences.
On the identical time, safety in web3 has additionally emerged as a formidable matter as customers should encounter various kinds of safety threats in web3. The issue with web3 is that you just can’t depend on the inherent safety rules of web3. For instance, the transparency of good contracts on public blockchains can expose various kinds of vulnerabilities to malicious brokers.
Web3 serves as a decentralized model of the net with a peer-to-peer community, the place customers gained’t want intermediaries resembling social media firms, tech giants, and banks. One of many foremost highlights in a web3 safety information would level on the elementary safety rules related to web3.
The safety rules in web3 embody cryptography, which facilitates encryption and safety for information. Equally, blockchain know-how gives a safe ledger for web3 transactions via immutability. Allow us to be taught extra about web3 safety and finest practices for safeguarding your digital belongings.
Significance of Safeguarding Digital Belongings in Web3
Earlier than searching for insights about finest practices for web3 safety, you could be taught in regards to the significance of safeguarding your digital belongings. The normal scope of cybersecurity revolved round securing digital belongings resembling information and folders that didn’t retailer something of financial worth. If a safety resolution can safeguard customers from downloading malicious software program or clicking on suspicious web sites, then it’s thought of a dependable software for cybersecurity.
Nevertheless, web3 has modified the definition of digital belongings with the arrival of cryptocurrencies and NFTs. Customers can depend on blockchain-based decentralized platforms for proudly owning, storing, and controlling digital belongings, together with cryptocurrencies and NFTs. In a manner, web3 turned the web right into a protected deposit field that permits creation, storage, and alternate of belongings with financial worth.
The decentralized model of the web launched new variants of safety dangers. Customers should be taught web3 safety rules and finest practices to keep away from their precious belongings from theft. You will need to do not forget that web3 removes intermediaries, and the duty of safeguarding digital belongings falls on the customers. Subsequently, you will need to perceive how web3 safety differs from web2 cybersecurity.
Study the basics, challenges and use instances of Web3.0 blockchain from Introduction To Web3 E-Ebook
Variations between Web2 and Web3 Safety
Once you evaluate web2 with web3 by way of safety, you can find that web2 safety breaches are momentary, and customers can resolve them simply. Then again, web3 safety dangers are more likely to have huge penalties for customers. For instance, safety breaches in web2 can result in lack of data, resembling names, bank card numbers, or addresses. Such kinds of assaults can result in publicity to delicate data on the web. Nevertheless, bank card firms may take responsive motion by freezing the playing cards and issuing new playing cards.
The ramifications of web3 are virtually irreversible owing to the immutable nature of blockchain. Moreover, breaches in web3 platforms may imply that 1000’s of customers may lose their digital belongings completely. Web3 safety breaches may additionally injury the status of web3 platforms, which may final for an prolonged interval.
The web3 cybersecurity infrastructure has a protracted option to go, as a lot of the web3 options depend on single-layer safety options. As a matter of reality, the full losses from web3 safety breaches within the first half of 2023 amounted to $655.61 million. Round 108 assaults have led to losses of just about $471 million. In 2022, the losses as a result of web3 safety breaches amounted to nearly $3.6 billion.

Definition of Web3 Safety
The issues with web3 safety and the large scale of losses as a result of web3 safety breaches have created curiosity about particular measures for safeguarding your digital belongings. The solutions to ‘What’s web3 safety?’ level to the completely different processes, programs, and methodologies applied for safeguarding decentralized applied sciences. Web3 safety envisions safety of blockchain-based platforms, decentralized apps, and the digital belongings of web3 customers.
The distributed mannequin utilized in web3 gives freedom from intermediaries, which improves privateness and transparency. Nevertheless, the transparency exposes web3 to various kinds of threats. As the recognition of DeFi and NFTs continues rising, you will need to search for robust safety measures to safeguard web3 options. You may safeguard your digital belongings in web3 with a transparent understanding of safety and privateness dangers.
Wish to discover an in-depth understanding of safety threats in DeFi tasks? Enroll now in DeFi Safety Fundamentals Course
What are the Notable Safety and Privateness Threats in Web3?
The perfect method to staying protected in opposition to an issue is to grasp the issue and the related dangers. With a complete understanding of web3 safety dangers, you’ll find the very best practices for resolving the threats. The dangers for web3 customers could be labeled into safety and privateness dangers. Allow us to be taught extra in regards to the frequent safety and privateness dangers you’ll find in web3.
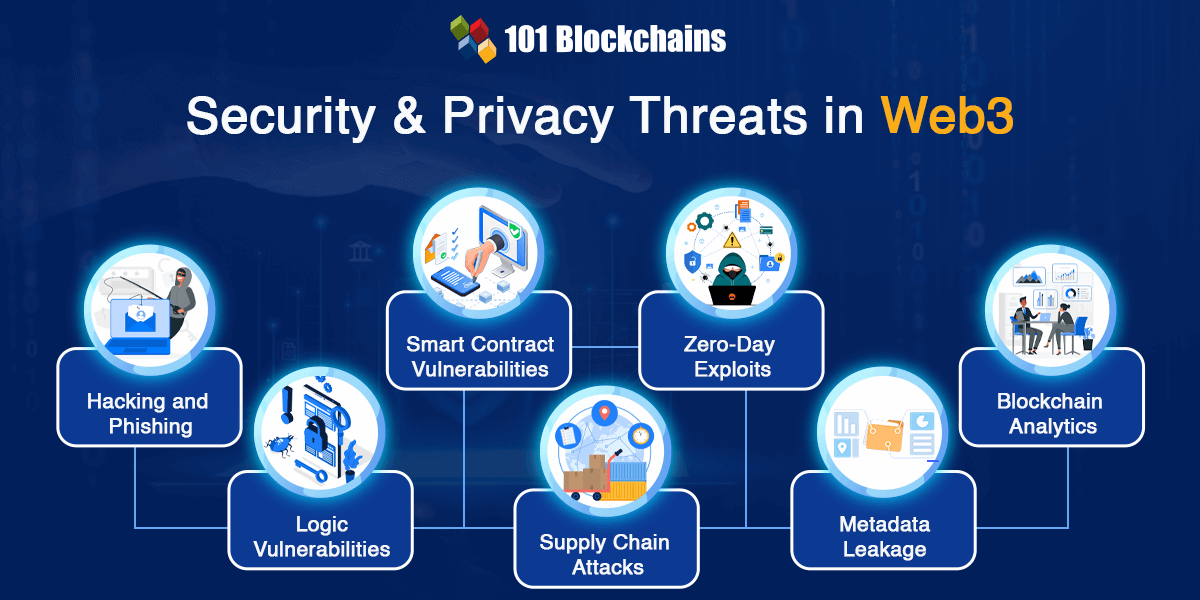
The 2 fashionable web2 assaults which discover their manner into discussions about web3 safety embody hacking and phishing. Any web3 safety information can be incomplete with out mentioning hacking and phishing assaults. Hackers may exploit the vulnerabilities within the dApp code logic or decentralized infrastructure to acquire unauthorized entry to personal keys, consumer wallets, and delicate information.
Phishing assaults work by deceiving customers in order that they will reveal their non-public keys or any delicate data. Phishing is without doubt one of the confirmed and efficient approaches that hackers use to achieve very important data from customers. You will need to be aware that hackers may use social engineering expertise for phishing assaults with out counting on technical information.
Sensible Contract Vulnerabilities
Web3 safety relies upon straight on safety of good contracts as they’re the core elements of the web3 ecosystem. Any particular person who needs to be taught web3 safety finest practices should familiarize themselves with good contracts and the way they work. Sensible contracts work as automated agreements or transactions that would run independently upon satisfying sure circumstances. Flaws within the good contract may result in unimaginable outcomes, resembling unintended actions and lack of funds.
Excited to be taught in regards to the crucial vulnerabilities and safety dangers in good contract growth, Enroll now within the Sensible Contracts Safety Course
Decentralized functions, or dApps, are additionally a core factor of the web3 ecosystem and will result in completely different safety dangers. dApps characteristic various kinds of vulnerabilities, together with backdoors and logic vulnerabilities that would open the doorways for hackers to take advantage of the contracts.
One other noticeable sort of assault in web3 refers to produce chain assaults during which attackers exploit a particular element of the web3 utility. For instance, attackers may exploit an open-source library applied within the code of a web3 utility.
Zero-day exploits additionally have an effect on safety in web3 by exposing a vulnerability inside the web3 neighborhood. It capitalizes on the ignorance a couple of particular vulnerability. Attackers may capitalize on such vulnerabilities to acquire unauthorized entry to programs, deploy malware, or steal information.
Web3 customers should additionally take note of privateness dangers resembling metadata leakage. Metadata refers back to the information that would expose essential details about consumer transactions, resembling sender and recipient addresses. You may surprise in regards to the issues with metadata for web3 cybersecurity with the immutability of blockchain. It’s true that nobody can modify the transaction information on blockchain. Nevertheless, malicious brokers can use the metadata of a transaction to attract inferences about delicate data of customers.
The issues for web3 safety additionally emerge from the revolutionary developments within the web3 ecosystem. Blockchain analytics makes use of information analytics strategies for tracing the transaction move on blockchain. It will probably serve promising outcomes for personalization of companies for web3 customers.
Then again, blockchain analytics may additionally expose delicate details about customers, together with the identification of the consumer and quantity of transactions. The chances of metadata leakage complement the dangers related to blockchain analytics by risking publicity to delicate information.

Finest Practices for Safeguarding Your Belongings in Web3
The listing of safety dangers in web3 is considerably intensive, and new kinds of safety dangers emerge daily. On the identical time, the rising adoption of web3 additionally makes it a promising goal for attackers. Cryptocurrencies, NFTs, digital actual property, and plenty of different belongings are making their manner into web3, which improves the worth of belongings locked within the web3 panorama. Listed below are a few of the finest practices you need to observe for securing your belongings in web3.
The most important threat in web3 is the specter of non-public key theft. Non-public keys provide help to acquire management over your cryptocurrency and digital belongings in web3. One of the best method for securing digital belongings is to stop anybody from accessing your non-public keys. Curiously, you possibly can depend on a {hardware} pockets for storing your cryptocurrencies and digital belongings with safety. {Hardware} wallets retailer your non-public keys in offline storage with bodily gadgets. Common examples of {hardware} wallets embody Trevor and Ledger. You can even make the most of the {hardware} wallets as a further layer for Metamask.
Observe Warning with the Restoration Phrase
The restoration phrase or seed phrase is one other essential piece of knowledge that you need to safeguard in any respect prices. The seed phrase features a mixture of 12 to 24 phrases, which may help in recovering your non-public keys. You’ll find references to safeguards for the seed phrase in responses to “What’s web3 safety?” as one of many frequent solutions for web3 safety. Do not forget that you need to by no means share your restoration phrase with anybody or retailer it on-line. You may write down the restoration phrase on a bit of paper and retailer it in a safe location that solely you possibly can entry.
Make the most of Two-Issue Authentication
One other confirmed advice for safeguarding your digital belongings in web3 is two-factor authentication. You may be taught web3 safety solely by following a few of the standard tenets in web2 cybersecurity. Two-factor authentication has served as an efficient layer of safety for web2 functions, and it may work in the identical manner for web3.
The second issue implies that you’d obtain a code in your cellphone or one generated by an authentication app. Two-factor authentication may assist in stopping unauthorized entry when somebody has compromised your password. Majority of web3 functions present the ability of two-factor authentication, and customers ought to all the time allow it in all instances.
Curious to develop an in-depth understanding of web3 utility structure? Enroll now within the Web3 Utility Improvement Course
How Can You Select the Proper Instruments for Securing Your Digital Belongings?
Web3 customers should take duty for securing digital belongings of their web3 expertise. Subsequently, you will need to choose the fitting instruments that would defend your digital belongings in opposition to safety threats. You may depend on efficient web3 safety software program to keep away from unwarranted compromises of your digital belongings. Listed below are a few of the options you need to search for in a software for securing web3 belongings.
To begin with, you could select web3 safety software program with real-time safety. The software program should present real-time transaction audits to establish dangerous logic alongside crucial vulnerabilities. As well as, it should even have a extremely responsive notification or reporting mechanism for warning customers.
One other essential requirement for safety in web3 would level to anti-phishing options. Phishing is a significant safety threat in web3, and anti-phishing options assist in simpler detection of phishing web sites. It may assist in blocking malicious web sites and safeguarding your precious belongings.
Most essential of all, the web3 safety software program should obtain common updates to establish newest threats. Updates are an essential requirement for guaranteeing efficient safeguards in opposition to rising threats to web3 safety.
Begin your journey to turning into an knowledgeable in Web3 safety expertise with the steering of trade consultants via Web3 Safety Knowledgeable Profession Path
Conclusion
One of the best practices for safeguarding your digital belongings in web3 would deal with stopping any vulnerabilities in good contract code. As well as, customers should additionally perceive the implications of various web3 safety dangers and their origins. Web3 is a quickly rising trade with the introduction of revolutionary options like NFTs, metaverse, and web3 video games. The excessive worth of belongings in web3 has turned web3 right into a searching floor for malicious actors.
On high of it, the profitable propositions for fast earnings in web3 may deceive customers into giving up delicate data. Subsequently, you will need to find out about web3 safety and the very best practices for shielding your belongings. Familiarize your self with the basics of web3 and establish how one can guarantee the very best safety on your web3 belongings.

*Disclaimer: The article shouldn’t be taken as, and isn’t supposed to offer any funding recommendation. Claims made on this article don’t represent funding recommendation and shouldn’t be taken as such. 101 Blockchains shall not be liable for any loss sustained by any one who depends on this text. Do your individual analysis!
[ad_2]
Source link
